For The King 2 Review – Co-op At Its Finest

Official Score
Overall - 95%
95%
For The King 2 is the perfect sequel. It takes the very best components of its predecessor and uses those time-tested elements to raise the series to new heights. To put it simply, For The King 2 is one of the best strategy-based co-op experiences on the market today.
It never feels like we get enough co-op games nowadays. I don’t mean all these always online multiplayer games as a service stuff, just good old-fashioned co-op fun. Developed by Iron Oak Games and Published by Curve Games, For The King 2 is a direct sequel to the 2017 original, offering players strategy-fueled turn-based combat with tabletop-inspired exploration and roguelite progression.
For The King 2 is an old-school sequel. It doesn’t try to reinvent the wheel or mash things up with an entire genre change. It simply takes everything that made the original game as fantastic as it was, and just adds more. We’ve got new random events, new locations, new classes, new weapons, all fantastic stuff but best of all? We can now bring in a 4th player.
For The King 2 Review

For The King’s original cap on three playable characters was, arguably, about the only thing I didn’t like in the original game. We always had a 4th in the wings waiting to play, doing dice rolls or a quick round of rock, paper, scissors to see who had to sit it out this time. If you’re more of a solo player or don’t have a 4th friend to bring, each of the 4 characters you choose can be controlled by any number of players.
Each player can control a single character or it can be divided with fewer players. For the entirety of our time in the game, both Johnny and I controlled two characters each. This is something I usually find off-putting in games. I like to have my main character and not bother controlling an “AI” but with the way the gear and classes function, it feels more like double the fun and not double the work.
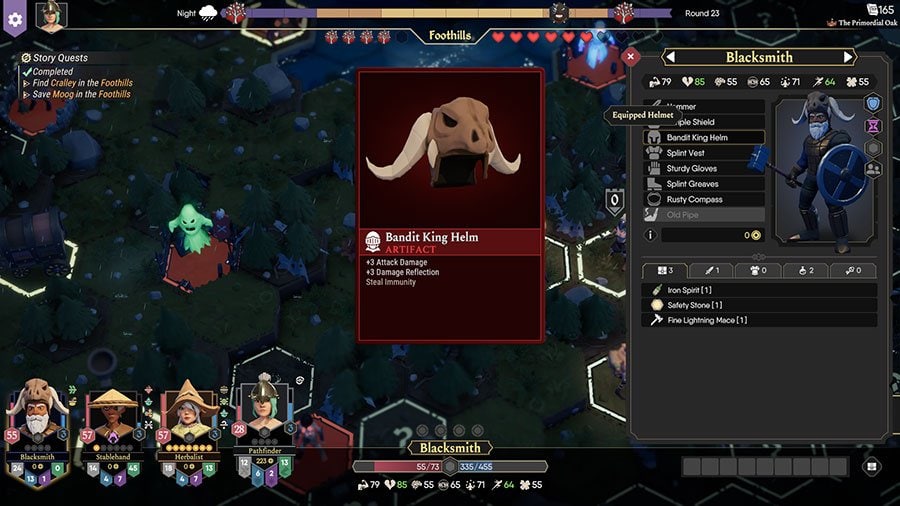
Each class comes with its own stats and individual abilities, typically a small random chance to do something useful and thematic for that class. The Blacksmith, for example, has an ability that will sometimes entirely negate the damage of an attack. The Alchemist has a small chance to brew potions at the end of each turn, basically grenades, and the Farmer sometimes creates a Scarecrow in battle that acts as a frontline tank. There is definitely some disparity between the classes, with some being so effective it’s stupid not to take them, and others being nigh on useless, but there’s enough variety of good classes for a ton of different party lineups.
Most of the classes excel in a couple of areas, making ideal builds and playstyles very apparent, but it’s not without flexibility either. You can play through different chapters with exactly the same class and party lineup and have different builds for most of the characters. Sometimes, this is by choice, other times you’re forced to adapt to the challenges you face.
The advancement and progress of each class is tied directly to the equipment you find in the game world. Tons of different weapon types, multiple defensive options between physical defense, magical defense, and evasion, it’s a system of mixed emotions. Sometimes you will find the perfect items, creating that ultra-powerful build you’d planned right at the start of the campaign. Other times one of your character struggle, falling behind the party because you’re not finding the perfect gear. This may sound somewhat disappointing but it’s the lows that really make the highs such a remarkable achievement.
Exploration remains a pillar of the For The King experience and remains largely unchanged in For The King 2, with good reason. When exploring the Overworld every hex hides possibility, it hides excitement. A brand new class, a powerful new weapon, a challenging battle, just a few potential discoveries with each shiny question marked hex that you explore. It’s a system that worked so well in the original and one that continues to be one of the game’s most appealing elements.
The challenge and difficulty of exploration lie within the efficiency and management of your party’s movement and locations. Allies can only join battles if they are within range, certain classes excel at avoiding enemy encounters while others struggle. It’s the careful planning and execution of an exploration plan that keeps turn after turn, an explorer’s dream. It sounds simple enough, right? Don’t start a battle unless all your allies are within range. Don’t go exploring with a class that is unable to sneak past an ambush. Those ideas are sound in principle, but then, something shiny.
And that’s all it takes. A new event appears, an enemy you’ve not fought before, a pot of gold at the end of a rainbow (literally and figuratively), and that’s it. One of your idiot friends has run off 7 hexes in the wrong direction to try and pull a sword out of a stone and your plans have gone to shit. Exploration is a constant test of risk vs. reward, made riskier by the friends you keep, and that’s without considering the constant threat and peril of a looming world event – one that may strengthen every enemy you encounter or steal items from your loot pools.
These world events can either be directly related to the story of a specific Chapter or Scourges, unique enemies that promise some of the most difficult battles in the entire game. This creates further tension as you need to balance exploration with controlling the worlds Chaos level, a timer-like system that’s difficult to manage, but very rewarding when you’re able to find the perfect mix of objectives and freedom. Considering the difficulty of these battles the rewards are often underwhelming, an issue the original game struggled to solve, but the satisfaction of taking down these difficult bosses nearly offsets the disappointment, nearly.
For The King 2’s combat system, on the other hand, has seen quite a number of improvements and changes, primarily, the combat grid. It’s a formation system that rewards tactical placement of specific characters in specific locations. Tanks and melee users excel on the frontlines, while magical and ranged users benefit from defensive bonuses on the back, there is a caveat however, it’s random. This was quite jarring initially, having to constantly move characters around to the correct locations but without the random element, the system becomes quite passive and relatively dull. It’s not a complete mess, the game won’t place your squishy guys on the frontline, but the lack of fixed formations may be off-putting for some.
After understanding its importance in creating a more dynamic combat environment, it’s a feature that grew on me as time went on. Toward the end, we understood that we’re not going to begin each fight in a perfect formation but neither is the enemy. Managing character locations to avoid area of effect attacks, careful placement of your buffing characters to maximize effectiveness, it’s another rock on this mountain of risk vs. reward that the game builds and relies on so heavily.
The core components of the combat system, attacks and abilities being tied to dice rolls based on specific stats, remains much of the same. It’s an experience of massive highs and incredible lows. Nailing that awesome 60% chance for an enormous strike is as satisfying as it gets, matched only by the utter dismay of missing a 95% chance to hit and having a character killed as a result. It’s a love hate relationship that creates memories and experiences that will last a long time.
The most exciting additions to For The King 2, that truly set it apart from its predecessor, is the inclusion of a loadout system and its roguelite elements. As you complete story objectives and dungeons you are rewarded with Lore Books, these Lore Books can then be spent in the Lore Store to unlock new items, classes, events, and cosmetics. Previously, this simply added stuff unlocked to the random pool of things to find in the next campaign but the new Loadout system makes unlocks far more effective.
At the beginning of any Chapter, you can assign a Loadout to each character in your party, using Loadout Points. These can be used to start with additional healing items, extra gold, stronger weapons and armor, it adds a level of strategy and tactical thinking that the previous game lacked. Being able to fine tune and plan your strategies for the earlier stages of the game is really engaging for the entire party and makes the previously predictable and often boring first few turns, more impactful and exciting.
Bringing in the best of the old with the creative direction of the new makes For The King 2 feel instantly familiar and charming, like coming back to a warm home after a cold days work. The addition of new combat and reward mechanics deliver the thrill of exploration and combat that only died down in the original after completing the entire game and running out of things to unlock.
For The King 2 is the perfect sequel. It takes the very best components of its predecessor and uses those time-tested elements to raise the series to new heights. To put it simply, For The King 2 is one of the best strategy-based co-op experiences on the market today.