Final Fantasy VII Rebirth Preview – Let’s Mosey

Cloud Strife, Tifa Lockhart, Aerith Gainsborough – gamers no doubt know these names better than their own kids’ since Final Fantasy VII revolutionized the JRPG space back in 1997.
2020’s Final Fantasy VII Remake set an incredible precedent as the first part of this fan-favorite trilogy, winning countless awards in its wake. With years of anticipation behind it, the upcoming release of Square Enix’s Final Fantasy VII Rebirth promises to carry the torch, leading players outside the stifling confines of Midgar into a vast open world filled with near endless possibilities.
Gamers Heroes got an in-depth session with Final Fantasy VII Rebirth at a recent press event, reuniting with a cast we have to know and love. For somebody who has played the original multiple times (and has an Editor-in-Chief with a Cloud profile picture), our time so far with Final Fantasy VII Rebirth feels incredibly fresh and full of possibilities, all while sharing the familiarity and camaraderie of a close friend.
Join us as we share some of the highlights with our Final Fantasy VII Rebirth preview:
Final Fantasy VII Rebirth Preview
Story
We were able to play through the first two chapters of Final Fantasy VII Rebirth, continuing the story of party members Cloud Strife, Barret Wallace, Tifa Lockhart, Aerith Gainsborough, and Red XIII.
This cinematic action RPG wastes no time, picking right back up from the party’s escape from Midgar in Final Fantasy VII Remake. There is a “Story So Far” section that can get players up to speed, but those who have previously joined AVALANCHE and its cause will be better prepared for the events that follow.
However, rather than focus on the here and now, the first chapter of Final Fantasy VII Rebirth looks back to the events that happened in Nibelheim five years ago.
It was truly a different time – SOLDIER Cloud Strife, joined by former brother-in-arms Sephiroth, are sent to this town the former member calls home. Rounding out the trio is the plucky Tifa Lockhart (complete with cowboy hat!), serving as their guide to the first Shinra reactor that’s located at Nibelheim’s summit. A treacherous climb, these three will have to contend with monsters, downed bridges, and other threats.
One might know these story beats from the title’s 1997 debut, but the events that transpire are presented in a brand-new light. For one, the power of the PlayStation 5 is on full display – monsters and mako reactors have never looked so good, with a presentation that manages to transform the polygonal and pre-rendered 32-bit landscapes to the modern era. However, it’s the way the story unfolds that will make even the most experienced SOLDIER on the edge of their seat. We won’t spoil the surprise(s), but take note this is far from a simple remake.

The Open World
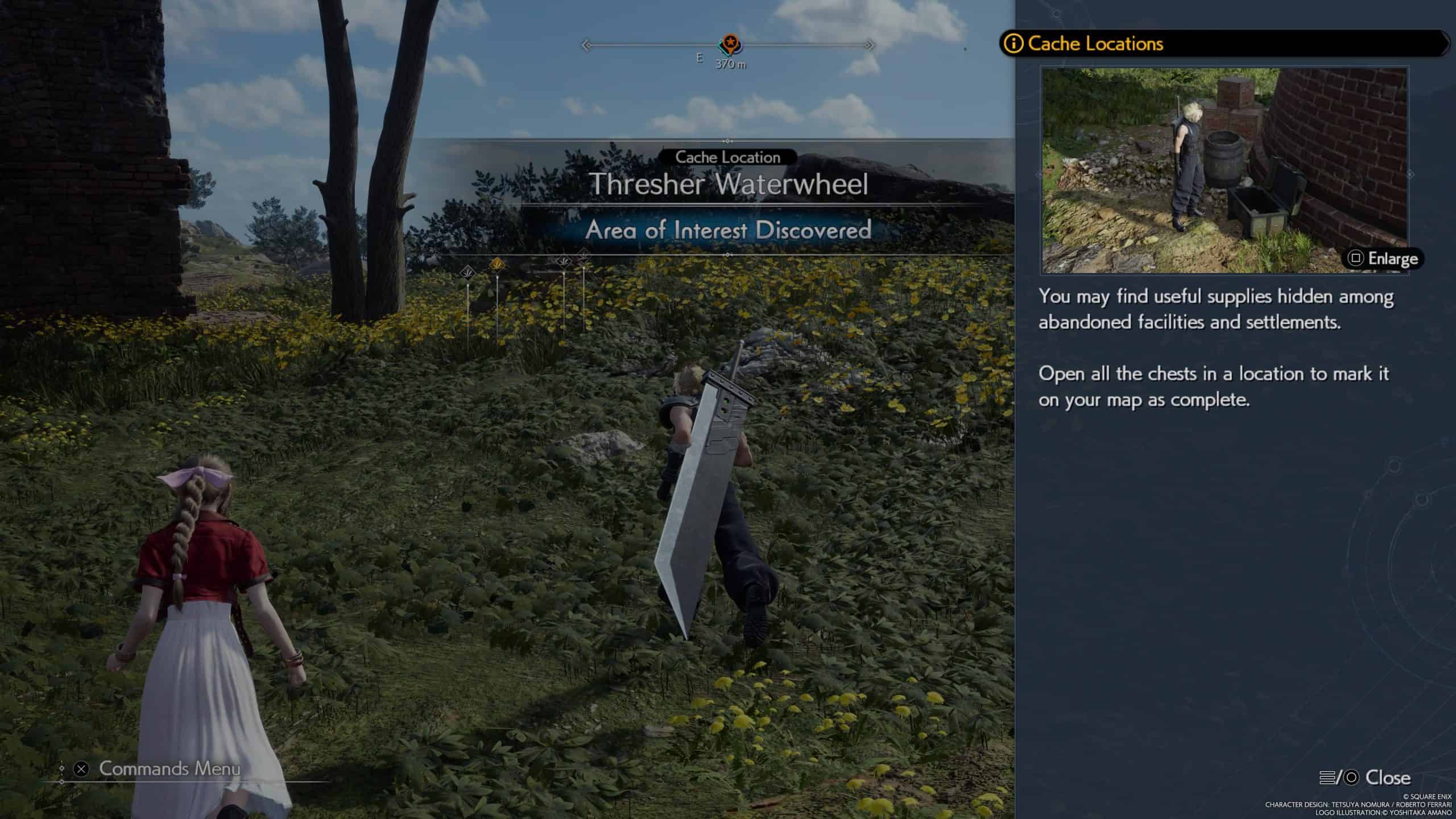
After leaving the idyllic (and aptly named) city of Kalm, players will soon be treated to a truly massive world in the form of the Grasslands.
This open-world area lives up to its size by giving players a wealth of activities to explore. No need to be lost (at least, no need if you don’t want to be) – there are plenty of quest markers that are conveniently located at the top of the map. Color-coded for easy access, players can easily see where the next major item lies as the crow flies.
However, while that is most certainly an option, that would be an absolute disservice to the sheer amount of content Final Fantasy VII Rebirth has on tap. There are plenty of things to discover as players fulfill their wanderlust, from crafting ingredients to treasure troves. As party member Barret Wallace says early on, pick any direction and walk forward!

Chocobo
Walking on foot is so four years ago, going the way of the dodo. Rather, the new bird in town is the iconic-feathered friend: the Chocobo!
After visiting Bill’s Chocobo Ranch in the Grasslands and tracking down Piko the Chocobo in an amusing minigame, these big ol’ yellow birds are at your beck and call with a single whistle – conveniently mapped to the R1 button.
Not only do they help players traverse murky swamps and add some pep to your step, they can also sniff out a bunch of goodies ripe for the taking – just the thing to boost your inventory! During our time with the preview, we loved traveling around in style, seeking out said goodies and getting used to the dynamics of our feathered friend.
Feel like a Chocobo is not quite fast enough? Final Fantasy VII Rebirth features a fast-travel system that is tied to a number of points of interest. Towns, repaired chocobo stops, and activated Remnawave Towers (more on that later) can all help players move from point A to point B with relative ease. It took us a fair amount of time to get from the outskirts of Kalm to Bill’s Chocobo Ranch, so for those looking to get a move on, this will prove to be just the thing one needs to jet set.

Community Noticeboards and Side Jobs
Providing that odd jobs aren’t just for Craigslist anymore, Cloud and co. can work hard for the money throughout Final Fantasy VII Rebirth.
For those wondering what lies in store, players will be able to check out Community Noticeboards to find new employers. Those that take on these side quests can get themselves a number of perks, including rare rewards, an increased party level, and even deeper bonds with one’s allies.
Of course, it wouldn’t be a Final Fantasy game without Quests! There’s also the occasional jobs that pop up throughout Final Fantasy VII Remake. Completing these hand-for-hire tasks will net players sweet, sweet Gil currency.
Chadley’s Intel
Returning to Final Fantasy VII Rebirth is cyborg and materia researcher Chadley, eager to have Cloud and his friends help him with his research around World Intel after their initial encounter in the Sector 7 slums of Midgar.
Remnawave Towers
Final Fantasy VII Rebirth’s world is massive, but there’s a way to get a clearer picture as to what the map has in store: Remnawave Towers.
Located throughout Final Fantasy VII Rebirth’s Grasslands, these towers help to show a number of points of interest once activated. Think of it as similar to the Sheikah Towers from Nintendo’s The Legend of Zelda: Breath of the Wild, providing a clearer picture of different regions of the map. This proves to be just the thing for players to uncover ruins, rare phenomena, and other points of interest that one will absolutely need to truly complete Final Fantasy VII Rebirth. As mentioned before, they also serve as a waypoint.
During our time with the game, we quickly came to realize that the Grasslands hide countless secrets. With each Remnawave towers activated by players, players will truly be able to see everything Final Fantasy VII Rebirth has to offer.
Lifesprings
As players travel far and wide, there are plenty of Lifesprings hidden away in the world of Final Fantasy VII Rebirth. While Shinra couldn’t care less about them, Chadley is all too eager to actively seek these areas out.
We ended up finding one of these Area of Interest in our journey – albeit with a little help from a springseeker owl. After sending the data over, we were able to get some Region Intel from the area that, in turn, provided additional worldbuilding. Chadley did mention that these lifesprings are in every region, so we look forward to truly immersing ourselves throughout our journey in the full release.
Combat Simulator 3.1.0
For those that like to test their might in Final Fantasy VII Remake, Chadley’s got just the thing: The Combat Simulator. With this virtual world, a number of Deities like the mighty Titan are ready to be summoned and subsequently taken down.
However, the devil is truly in the details. While players can net themselves some valuable prizes like summoning materia of these fearsome foes, they also default to their full power the first time one challenges them. We ultimately learned this the hard way during our session, resulting in a situation we’d rather not relive.
It’s not all doom and gloom, however; there is a way to get an edge. By analyzing summon crystals around the world, players can lower the power of the enemies of the Combat Simulator by a magnitude of three. In a nutshell: The more summon crystals you find, the easier they become. In other words, it pays to explore!

Queen’s Blood
It just wouldn’t be a Final Fantasy title without a minigame that promises to absolutely consume one’s life and rack up those play hours. In Final Fantasy VII Rebirth, players will be able to find their heart in the cards with the release of Queen’s Blood. Getting a deck early on, players will be able to challenge people (and little girls with stuffed animals) the world over, building the perfect set of cards as things progress.
However, this is far from a simple repeat from Final Fantasy VIII’s Triple Triad.
Queen’s Blood tasks players with taking turns as they place cards down in one of three different lanes. Each card has its own point value, with the power of each card placed added to one’s lane total. However, players must keep the emerald pawns in mind, as they correspond with which cards go where. Whoever has the most points in each lane wins that corresponding pot, with the highest total points winning the game.
However, Queen’s Blood has a number of wrinkles that add some serious depth. For one, positions can rise in rank, which is a key part in commanding the board and getting the upper hand against one’s opponent. In addition, certain cards have certain abilities, meaning that carefully planning one’s loadout at the beginning of each match is an absolute must.
While we spent approximately five hours with Final Fantasy VII Rebirth, truly living out our (final) fantasies in the process. Despite this, we still have so much more we want to uncover, and are eager to play more and see what lies next for Cloud Strife and his party.
Fans can experience all of these elements – and then some – when Final Fantasy VII Rebirth releases for the PlayStation 5 on February 29, 2024.